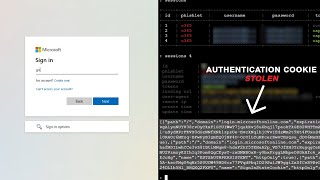
how mfa bypass attacks work
Published 1 year ago • 173 plays • Length 6:28Download video MP4
Download video MP3
Similar videos
-
 10:22
10:22
how voice cloning is used in social engineering and mfa bypass attacks
-
 4:18
4:18
how criminals bypass multi-factor authentication (mfa)
-
 3:55
3:55
mfa fatigue attacks - how mfa is bypassed
-
 3:58
3:58
attacker in the middle - how mfa is bypassed
-
 7:31
7:31
case study: the 2022 uber breach - an mfa fatigue attack
-
 3:00
3:00
attacker in the endpoint - how mfa is bypassed
-
 9:22
9:22
mfa can be easily bypassed - here's how
-
 44:07
44:07
how attackers can bypass phishing-resistant mfa | use these protections!
-
 2:47
2:47
mfa aitm attack
-
 9:20
9:20
how hackers bypass two-factor authentication (2fa)?!
-
 54:46
54:46
how hackers go from zero to takeover
-
 1:19
1:19
mfa bypass technique shared for fraud - this month in security
-
 38:35
38:35
how to set up microsoft multi-factor authentication (mfa)
-
 16:59
16:59
how hackers bypass 2 step verification
-
 8:13
8:13
is mfa still safe? | how hackers bypass mfa
-
 0:50
0:50
what is mfa fatigue attack? | mfa spamming: bypassing two factor authentication | admindroid
-
 38:21
38:21
how to set up duo multi-factor authentication (mfa)