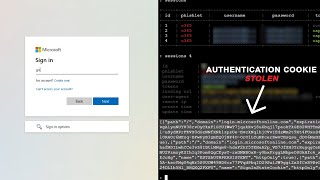
attacker in the endpoint - how mfa is bypassed
Published 1 year ago • 86 plays • Length 3:00Download video MP4
Download video MP3
Similar videos
-
 3:58
3:58
attacker in the middle - how mfa is bypassed
-
 3:11
3:11
0ktapus - how mfa is bypassed
-
 3:55
3:55
mfa fatigue attacks - how mfa is bypassed
-
 5:22
5:22
how attackers bypass mfa (multi-factor authentication) - security simplified
-
 1:27
1:27
how do attackers bypass mfa?
-
 4:20
4:20
evilginx attack demo: how hackers bypass microsoft mfa
-
 9:20
9:20
how hackers bypass two-factor authentication (2fa)?!
-
 10:06
10:06
how to bypass mfa - a real time example (it's easy)
-
 5:38
5:38
microsoft 365 security basics: mfa fraud alert
-
 6:28
6:28
how mfa bypass attacks work
-
 5:29
5:29
does mfa stop 99% of attacks? - cybersecurity mythbusters
-
 4:18
4:18
how criminals bypass multi-factor authentication (mfa)
-
![how hackers bypass mfa? [2 ways to stop them]](https://i.ytimg.com/vi/NsdkxvSSRoo/mqdefault.jpg) 8:34
8:34
how hackers bypass mfa? [2 ways to stop them]
-
 0:57
0:57
how to bypass mfa in web apps (educational)
-
 42:01
42:01
threats from the wild - episode 3: multi-factor authentication (mfa) bypass 101
-
 8:13
8:13
is mfa still safe? | how hackers bypass mfa
-
 1:00
1:00
09 06 2024 how hackers bypass mfa and what you can do about it
-
 13:40
13:40
mfa bypass via phishing: how attackers exploit weaknesses and what you can do
-
 9:22
9:22
mfa can be easily bypassed - here's how
-
 1:31:23
1:31:23
beyond the endpoint: a deep dive into using identity as the basis for incident response
-
 55:14
55:14
why you have an mfa emergency