protecting message integrity
Published 9 years ago • 945 plays • Length 1:01Download video MP4
Download video MP3
Similar videos
-
 1:05
1:05
protecting message confidentiality and integrity
-
 0:21
0:21
lesson introduction
-
 22:34
22:34
message integrity, message authentication and hash functions
-
 2:04
2:04
encrypting a large message
-
 8:12
8:12
hashing algorithms and security - computerphile
-
 4:07
4:07
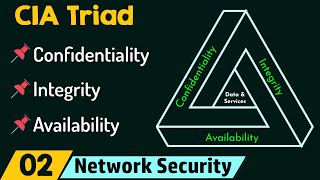
what is the cia triad
-
 10:17
10:17
what are digital signatures? - computerphile
-
 11:40
11:40
driving ethics & business integrity with data
-
 1:55
1:55
information security - integrity
-
 16:08
16:08
cia triad
-
 55:31
55:31
data integrity and information integrity - they are enterprise not just ciso issues
-
 21:31
21:31
lecture 51: message integrity & authentication | computer networks
-
 42:30
42:30
integrity policy enforcement: full system integrity verification - deven bowers, microsoft
-
 3:36
3:36
digital signatures
-
 3:48
3:48
policy look: data breaches
-
 5:37
5:37
user privacy & data integrity
-
 12:45
12:45
integrity and protection of data
-
 11:09
11:09
message integrity and message authentication
-
 4:03
4:03
protecting all your data with identity governance
-
 9:56
9:56
security 101: securing data by location
-
 15:55
15:55
09a information security