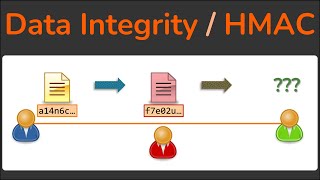
message integrity, message authentication and hash functions
Published 4 years ago • 3.4K plays • Length 22:34Download video MP4
Download video MP3
Similar videos
-
 6:12
6:12
#33 message authentication & authentication functions in cryptography |cns|
-
 7:24
7:24
data integrity - how hashing is used to ensure data isn't modified - hmac - cryptography
-
 30:26
30:26
types of authentication || message encryption || message authentication code || hash functions
-
 15:37
15:37
4.1 message integrity & cryptographic hash functions
-
 14:37
14:37
digital signatures, message integrity, and authentication | computer networks ep 8.3 | kurose & ross
-
 10:47
10:47
hash function | s8 ece | secure communication
-
 17:00
17:00
message authentication code-mac-requirements-uses-ktucst433 security in computing s7cs- mod 4 part 3
-
 47:40
47:40
message integrity and message authentication part-2 & basics of cryptographic hash functions
-
 16:47
16:47
cryptography: message integrity
-
 26:44
26:44
message integrity and authentication
-
 40:57
40:57
network security - types of authentication (message encryption, mac, hash functions)
-
 11:09
11:09
message integrity and message authentication
-
 9:35
9:35
message integrity in cryptography | message digest
-
 7:17
7:17
data integrity and hash function
-
 1:21
1:21
16. message authentication code mac
-
 21:31
21:31
lecture 51: message integrity & authentication | computer networks
-
 0:29
0:29
hmac - hash-based message authentication code
-
 22:49
22:49
cryptographic hash functions | hmac | sha
-
 16:37
16:37
message authentication using hash functions - network security
-
 7:08
7:08
lecture11 data security e: message authentication and hash functions 1
-
 7:13
7:13
#35 mac ( message authentication code ) - working and significance |cns|