role-based and mandatory access control (its335, l11, y14)
Published 9 years ago • 19K plays • Length 32:36Download video MP4
Download video MP3
Similar videos
-
 41:27
41:27
linux permissions examples (its335, l11, y14)
-
 26:05
26:05
introduction to access control (its335, lecture 9b, 2013)
-
 45:10
45:10
access control (its335, l10, y14)
-
 20:39
20:39
explain access control models| discretionary dac, mandatory mac, rbac, rule, attribute, risk based
-
 24:12
24:12
відеоінструкція з підключення та додавання карток у комплектах контролю доступу seven systems
-
 8:40
8:40
discover the benefits of modern security access control systems
-
 9:34
9:34
what is access control system | working | type of reader | imp video for interview q & a | in hindi
-
 3:30
3:30
security - role based access control rbac
-
 8:00
8:00
role-based access control (rbac) explained: how it works and when to use it
-
 2:35
2:35
mandatory access control (mac) models
-
 4:06
4:06
mandatory access controls (mac), bell-lapadula, and biba explained.
-
 4:50
4:50
role based access control
-
 1:17:03
1:17:03
access control and linux permissions (its335, lecture 10, 2013)
-
 3:07
3:07
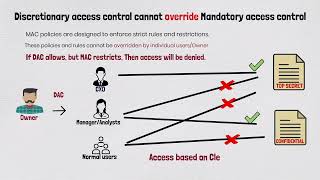
access control models: why discretionary access control cannot override mandatory access control?
-
 1:04:25
1:04:25
access control (its335, l08, y15)
-
 1:12
1:12
discretionary access control
-
 10:04
10:04
access control - sy0-601 comptia security : 3.8
-
 1:17:44
1:17:44
malicious software (its335, l11, y14)
-
 13:17
13:17
ac-5 - separation of duties - access controls in baselines - cup of cyber