usenix security '15 - under-constrained symbolic execution: correctness checking for real code
Published 2 years ago • 446 plays • Length 30:15Download video MP4
Download video MP3
Similar videos
-
 11:08
11:08
usenix security '20 - symbolic execution with symcc: don't interpret, compile!
-
 26:59
26:59
usenix security '15 - verified correctness and security of openssl hmac
-
 26:50
26:50
usenix security '15 - taintpipe: pipelined symbolic taint analysis
-
 28:24
28:24
usenix atc '13 - redundant state detection for dynamic symbolic execution
-
 11:57
11:57
usenix security '20 - sys: a static/symbolic tool for finding good bugs in good (browser) code
-
 23:42
23:42
usenix security '18 - qsym : a practical concolic execution engine tailored for hybrid fuzzing
-
 13:22
13:22
usenix security '22 - ferry: state-aware symbolic execution for exploring state-dependent program
-
 5:36
5:36
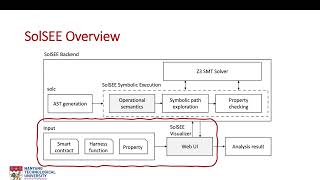
solsee: a source-level symbolic execution engine for solidity
-
 28:39
28:39
usenix security '15 - measuring real-world accuracies and biases in modeling password guessability
-
 27:35
27:35
usenix security '15 - you shouldn’t collect my secrets: thwarting sensitive keystroke leakage...
-
 23:16
23:16
usenix security '15 - supor: precise and scalable sensitive user input detection for android apps
-
 20:15
20:15
usenix security '19 - antifuzz: impeding fuzzing audits of binary executables
-
 27:37
27:37
usenix security '15 - a measurement study on co-residence threat inside the cloud
-
 1:29:37
1:29:37
usenix security '15 - perspectives on securing cyberspace
-
 23:56
23:56
usenix security '18-inception: system-wide security testing of real-world embedded systems software
-
 21:41
21:41
usenix security '18 - formal security analysis of neural networks using symbolic intervals
-
 24:24
24:24
symbolic execution with symcc - don't interpret, compile!