usenix security '16 - finding and fixing security bugs in flash
Published 2 years ago • 60 plays • Length 1:04:31Download video MP4
Download video MP3
Similar videos
-
 22:59
22:59
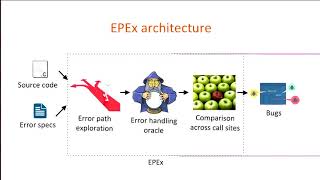
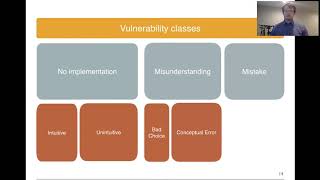
usenix security '16 - automatically detecting error handling bugs using error specifications
-
 25:23
25:23
usenix security '16 - harvesting inconsistent security configurations in custom android roms...
-
 1:18:41
1:18:41
usenix security '16 - crashing drones and hijacked cameras: cybertrust meets cyberphysical
-
 23:41
23:41
usenix security '16 - undermining information hiding (and what to do about it)
-
 12:58
12:58
usenix security '23 - remote code execution from ssti in the sandbox: automatically detecting and...
-
 11:58
11:58
usenix security '21 - finding bugs using your own code: detecting functionally-similar yet
-
 11:20
11:20
usenix security '23 - the most dangerous codec in the world: finding and exploiting...
-
 10:39
10:39
security testing with snyk.io || scan security issues directly from code
-
 6:05
6:05
how to find a working bug host | sni | server name indication | working sni | v2ray |worldwide
-
 6:41
6:41
fix zipalign error, libunwind, libbacktrace, msfvenom, evildroid, fatrat, embedding payload in apks
-
 13:01
13:01
usenix security '23 - place your locks well: understanding and detecting lock misuse bugs
-
 12:05
12:05
usenix security '23 - silent bugs matter: a study of compiler-introduced security bugs
-
 12:07
12:07
usenix security '20 - understanding security mistakes developers make: qualitative analysis...
-
 10:37
10:37
usenix security '20 - fuzzing error handling code using context-sensitive software fault injection
-
 12:25
12:25
usenix security '23 - whip: improving static vulnerability detection in web application by...
-
 27:59
27:59
usenix security '16 - thoth: comprehensive policy compliance in data retrieval systems
-
 30:15
30:15
usenix security '15 - under-constrained symbolic execution: correctness checking for real code
-
 12:51
12:51
usenix security '20 - firmscope: automatic uncovering of privilege-escalation vulnerabilities
-
 13:38
13:38
usenix security '23 - detecting api post-handling bugs using code and description in patches
-
 30:44
30:44
usenix security '16 - hey, you have a problem: on the feasibility of large-scale web vulnerability
-
 12:25
12:25
usenix security '22 - how to abuse and fix authenticated encryption without key commitment