usenix security '16 - the unfalsifiability of security claims
Published 2 years ago • 226 plays • Length 1:27:40Download video MP4
Download video MP3
Similar videos
-
 26:12
26:12
usenix security '16 - all your queries are belong to us: the power of file-injection attacks...
-
 23:41
23:41
usenix security '16 - undermining information hiding (and what to do about it)
-
 28:38
28:38
usenix security '16 - identifying and characterizing sybils in the tor network
-
 21:41
21:41
usenix security '18 - formal security analysis of neural networks using symbolic intervals
-
 12:46
12:46
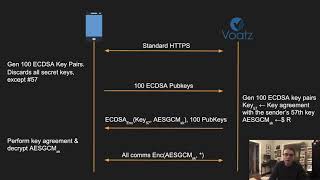
usenix security '20 - the ballot is busted before the blockchain: a security analysis of voatz
-
 1:18:41
1:18:41
usenix security '16 - crashing drones and hijacked cameras: cybertrust meets cyberphysical
-
 1:01:06
1:01:06
usenix security '16 - report from the field: a cdn's role in repelling attacks against banking...
-
 2:46:21
2:46:21
usenix security '16 - when governments attack: malware targeting activists, lawyers, and journalists
-
 31:48
31:48
usenix security '16 - zxcvbn: low-budget password strength estimation
-
 21:06
21:06
usenix security '14 - password managers: attacks and defenses
-
 12:03
12:03
usenix security '23 - know your cybercriminal: evaluating attacker preferences by measuring...
-
 21:55
21:55
usenix security '16 - the cut-and-choose game and its application to cryptographic protocols
-
 1:56:53
1:56:53
usenix security '16 - security competitions
-
 1:47:42
1:47:42
usenix security '16 - the moral character of cryptographic work
-
 27:27
27:27
usenix security '16 - request and conquer: exposing cross-origin resource size
-
 1:25:53
1:25:53
usenix security '16 - making https the default in the world's largest bureaucracy
-
 29:27
29:27
usenix security '16 - überspark: enforcing verifiable object abstractions for automated...
-
 11:20
11:20
usenix security '21 - when malware changed its mind: an empirical study of variable program behavior
-
 28:19
28:19
usenix security '16 - stealing machine learning models via prediction apis
-
 25:41
25:41
usenix security '15 - control-flow bending: on the effectiveness of control-flow integrity
-
 26:49
26:49
usenix security '16 - flowfence: practical data protection for emerging iot application frameworks