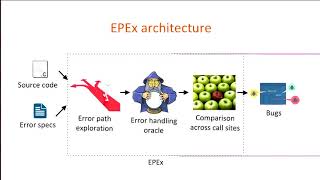
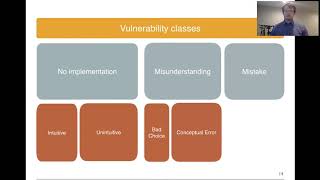
usenix security '21 - exposing new vulnerabilities of error handling mechanism in can
Published 2 years ago • 366 plays • Length 12:13Download video MP4
Download video MP3
Similar videos
-
 12:14
12:14
usenix security '21 - understanding and detecting disordered error handling with precise function
-
 12:05
12:05
usenix security '21 - an analysis of speculative type confusion vulnerabilities in the wild
-
 22:59
22:59
usenix security '16 - automatically detecting error handling bugs using error specifications
-
 11:53
11:53
usenix security '21 - automated discovery of denial-of-service vulnerabilities in connected vehicle
-
 10:37
10:37
usenix security '20 - fuzzing error handling code using context-sensitive software fault injection
-
 12:18
12:18
usenix security '21 - share first, ask later (or never?) studying violations of gdpr's explicit
-
 13:10
13:10
usenix atc '21 - tcp-fuzz: detecting memory and semantic bugs in tcp stacks with fuzzing
-
 14:33
14:33
rethinking searchable symmetric encryption
-
 11:47
11:47
usenix security '22 - pre-hijacked accounts: an empirical study of security failures in user account
-
 9:34
9:34
usenix security '23 - icspatch: automated vulnerability localization and non-intrusive...
-
 12:07
12:07
usenix security '20 - understanding security mistakes developers make: qualitative analysis...
-
 11:30
11:30
usenix security '23 - network detection of interactive ssh impostors using deep learning
-
 17:45
17:45
usenix enigma 2022 - auditing data privacy for machine learning
-
 11:34
11:34
usenix security '21 - canary - a reactive defense mechanism for controller area networks based
-
 22:43
22:43
usenix security '18 - precise and accurate patch presence test for binaries
-
 11:17
11:17
usenix security '23 - instructions unclear: undefined behaviour in cellular network specifications
-
 10:50
10:50
usenix security '21 - hiding the access pattern is not enough: exploiting search pattern leakage...
-
 32:47
32:47
usenix security '17 - hacking in darkness: return-oriented programming against secure enclaves