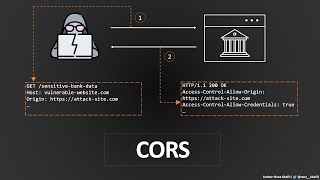
14- vulnerabilities - cross-origin resource sharing (cors)
Published 3 years ago • 3.2K plays • Length 12:45Download video MP4
Download video MP3
Similar videos
-
 5:41
5:41
cross origin resource sharing (cors) vulnerability | bugbountytraining | bug bounty service
-
 52:17
52:17
cross-origin resource sharing (cors) | complete guide
-
 2:31
2:31
cors in 100 seconds
-
 6:06
6:06
learn cors in 6 minutes
-
 2:53
2:53
what are cross-origin resource sharing (cors) vulnerabilities | owasp top 10 | bug bounty service
-
 10:46
10:46
cross-origin resource sharing (cors) | portswigger | hacksudo
-
 4:26
4:26
corsscanner fast cors misconfiguration vulnerabilities scanner🍻
-
 1:00
1:00
what is cors? blocked by cors policy error explained
-
 8:26
8:26
what is cors? | cross-origin resource sharing | cors explained!
-
 0:27
0:27
react proxy | easiest fix to cors errors
-
 9:31
9:31
hands-on guide to cors
-
 0:21
0:21
cve-2019-16517 - connectwise control - cross-origin resource sharing (cors) misconfiguration
-
 16:41
16:41
cors - lab #1 cors vulnerability with basic origin reflection | long video
-
 8:55
8:55
demystifying cors vulnerabilities: how attackers exploit cors to steal api keys
-
 1:31
1:31
insecure cors configuration vulnerability description | poc
-
 2:58
2:58
what is cross-origin resource sharing (cors)?
-
 4:39
4:39
lab: cors vulnerability with trusted null origin
-
 7:08
7:08
cors vulnerability detection on live application | awapt training hacker associate