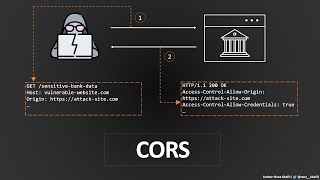
covering the under rated vulnerabilities: cors misconfiguration #1
Published 3 weeks ago • 2.9K plays • Length 17:19Download video MP4
Download video MP3
Similar videos
-
 5:41
5:41
cross origin resource sharing (cors) vulnerability | bugbountytraining | bug bounty service
-
 2:24
2:24
cors misconfiguration poc || bug bounty poc
-
 1:50
1:50
exploiting cors misconfiguration
-
 1:27
1:27
cors misconfiguration | leads to sensitive information | bug bounty poc
-
 2:51
2:51
cors || bypass cors misconfiguration leads to sensitive exposure poc || cashfree || bug bounty
-
 2:31
2:31
cors in 100 seconds
-
 1:47
1:47
$$$ bounty | insecure cors misconfiguration with full exploitation | bug bounty poc |
-
 52:17
52:17
cross-origin resource sharing (cors) | complete guide
-
 3:27
3:27
$15,000 bounty : remote code execution via file upload vulnerability | poc | bug bounty 2023
-
 12:59
12:59
the hidden csrf vulnerability: why testing every endpoint matters! (a must-watch lesson) | 2024
-
 9:20
9:20
cross site request forgery - computerphile
-
 6:06
6:06
learn cors in 6 minutes
-
 5:00
5:00
cors vulnerability mass hunting on dell bounty program worth 500$ | bug bounty poc
-
 1:20
1:20
cors exploit
-
 2:18
2:18
🛑 cors misconfiguration
-
 8:58
8:58
cors misconfiguration in tamil | bug bounty | shaz university
-
 13:04
13:04
chaining vulnerabilities: reflected xss cors = more impact!! | live demonstration | 2024
-
 2:33
2:33
cors vulnerability in facebook | bug bounty poc
-
 9:39
9:39
what is cors vulnerability | cors misconfiguration explain
-
 15:34
15:34
cors exploit ( the proper way ). 2 methods for cors detection and exploit for bug bounty hunters
-
 0:21
0:21
cve-2019-16517 - connectwise control - cross-origin resource sharing (cors) misconfiguration
-
 1:37
1:37
exploiting cors misconfiguration using xss