cryptographic hash function solution - applied cryptography
Published 12 years ago • 2.3K plays • Length 2:23Download video MP4
Download video MP3
Similar videos
-
 3:28
3:28
cryptographic hash function - applied cryptography
-
 1:34
1:34
hash collision solution - applied cryptography
-
 1:59
1:59
hash chain solution - applied cryptography
-
 8:12
8:12
hashing algorithms and security - computerphile
-
 17:04
17:04
hashing technique - simplified
-
 1:22:01
1:22:01
21. cryptography: hash functions
-
 0:30
0:30
hashing and eke solution - applied cryptography
-
 0:52
0:52
proofs of work - applied cryptography
-
 0:19
0:19
bitcoin solution - applied cryptography
-
 1:15
1:15
one way function - applied cryptography
-
 1:37
1:37
padding solution - applied cryptography
-
 1:26
1:26
hash chain - applied cryptography
-
 0:54
0:54
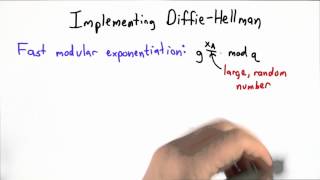
implementing dh - applied cryptography
-
 7:08
7:08
what is a cryptographic hashing function? (example purpose)
-
 3:14
3:14
hash function - cs101 - udacity
-
 0:46
0:46
random oracle solution - applied cryptography
-
 0:25
0:25
salted password scheme solution - applied cryptography
-
 0:36
0:36
provide scarcity solution - applied cryptography
-
 0:47
0:47
hashing and eke - applied cryptography
-
 1:42
1:42
weak collision resistance solution - applied cryptography