salted password scheme solution - applied cryptography
Published 12 years ago • 2.7K plays • Length 0:25Download video MP4
Download video MP3
Similar videos
-
 1:56
1:56
salted password scheme - applied cryptography
-
 2:16
2:16
storing passwords solution - applied cryptography
-
 2:38
2:38
storing passwords - applied cryptography
-
 52:55
52:55
4. hashing
-
 8:56
8:56
salting, peppering, and hashing passwords
-
 19:38
19:38
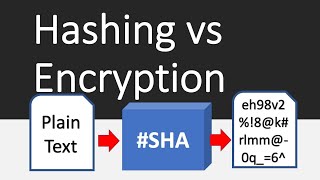
hashing vs encryption differences
-
 0:50
0:50
eke authentication solution - applied cryptography
-
 4:30
4:30
password hashing, salts, peppers | explained!
-
 1:23
1:23
password reuse - applied cryptography
-
 1:04:30
1:04:30
the encryption and password hashing recipe (with a little salt)
-
 1:59
1:59
hash chain solution - applied cryptography
-
 59:57
59:57
3. applied cryptography and trust: hashing methods (csn11131)
-
 10:16
10:16
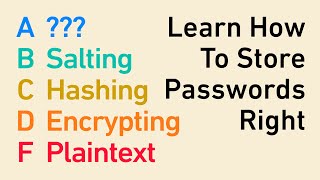
password storage tier list: encryption, hashing, salting, bcrypt, and beyond
-
 0:58
0:58
what is a salted password? can salted passwords be cracked? latest video
-
 0:59
0:59
hashing salts solution - web development
-
 0:41
0:41
public key cryptography solution - applied cryptography
-
 0:30
0:30
hashing and eke solution - applied cryptography
-
 18:18
18:18
adding salt to hashing: a better way to store passwords
-
 1:35
1:35
ssh authentication solution - applied cryptography