encrypt outputs - applied cryptography
Published 9 years ago • 2.5K plays • Length 0:49Download video MP4
Download video MP3
Similar videos
-
 1:15
1:15
encrypt outputs solution - applied cryptography
-
 2:53
2:53
file encryption solution - applied cryptography
-
 2:33
2:33
file encryption - applied cryptography
-
 1:00
1:00
permute outputs - applied cryptography
-
 12:33
12:33
cryptography: crash course computer science #33
-
 11:55
11:55
7 cryptography concepts every developer should know
-
 8:17:38
8:17:38
cryptography full course part 1
-
 1:58
1:58
question 1 - applied cryptography
-
 0:55
0:55
output feedback mode - applied cryptography
-
 3:13
3:13
counter mode - applied cryptography
-
 5:53
5:53
demo - applied cryptography
-
 3:33
3:33
summary - applied cryptography
-
 2:23
2:23
cryptographic hash function solution - applied cryptography
-
 2:32
2:32
advanced encryption standard - applied cryptography
-
 0:52
0:52
proofs of work - applied cryptography
-
 0:26
0:26
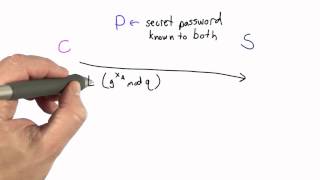
eke authentication - applied cryptography
-
 0:48
0:48
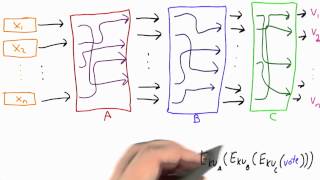
mixnet - applied cryptography
-
 2:55
2:55
encrypted key exchange - applied cryptography
-
 6:15
6:15
lorenz cipher machine - applied cryptography
-
 0:31
0:31
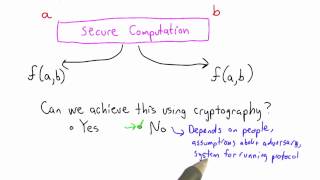
secure computation solution - applied cryptography