history of cyber kill chain | steps of cyber kill chain | pros and cons of cyber kill chain
Published 1 year ago • 690 plays • Length 47:41Download video MP4
Download video MP3
Similar videos
-
 2:05
2:05
cyber kill chain: what it is, how it works
-
 13:39
13:39
cyber kill chain | cyber kill chain explain | what is cyber kill chain? kill chain | cybersecurity
-
 14:55
14:55
real hacking: learn the cyber kill chain
-
 7:31
7:31
what is cyber kill chain # the 7 steps of a cyberattack
-
 1:58
1:58
what are the 7 phases of the cyber kill chain?
-
 6:44
6:44
the cyber kill chain
-
 15:38
15:38
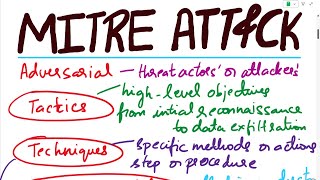
attack frameworks - cyber kill chain, mitre att&ck, diamond model of intrusion analysis
-
 16:43
16:43
mitre attack | mitre att&ck | mitre att&ck explained with an example | mitre att&ck analysis
-
 1:01:37
1:01:37
the kill chain: defending america in the future of high-tech warfare
-
 13:18
13:18
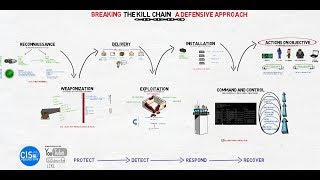
breaking the kill chain: a defensive approach
-
 1:02:56
1:02:56
mastering scs 9001: enhancing supply chain security in the face of cyber threats | webinar
-
 2:03
2:03
what is cyber kill chain? | all 7 steps explained
-
 4:42
4:42
learn the basics of the cyber kill chain
-
 57:58
57:58
cyber kill chain: the anatomy of a cyber attack
-
 22:28
22:28
cyber kill chain guide - how to improve cybersecurity posture
-
 8:28
8:28
cyber kill chain framework | cyber voyage | in tamil
-
 2:40
2:40
the cyber kill chain explained with real examples (2024)
-
 11:35
11:35
the cyber kill chain | how hackers do what they do
-
 7:04
7:04
what is cyber kill chain ?
-
 6:35
6:35
understanding the cyber kill chain and mitre att&ck | @sh3ll_5h0ck
-
 1:04
1:04
what is the cyber kill chain?