malicious software (its335, l10, y15)
Published 8 years ago • 1.5K plays • Length 1:12:26Download video MP4
Download video MP3
Similar videos
-
 41:12
41:12
malicious software and countermeasures (its335, l11, y15)
-
 1:14:18
1:14:18
malicious software (its335, lecture 11, 2013)
-
 48:11
48:11
malicious software and phishing (its335, lecture 12, 2013)
-
 1:17:44
1:17:44
malicious software (its335, l11, y14)
-
 46:38
46:38
attacks on digital certificates (its335, l21, y15)
-
 27:44
27:44
browsing, http and web applications (its335, l18, y15)
-
 1:12:05
1:12:05
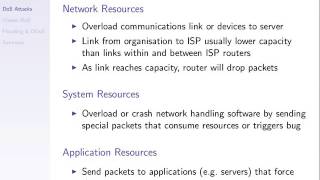
denial of service attacks (its335, l12, y15)
-
 8:47
8:47
virus.msword.sector
-
 3:52
3:52
check your computer for malicious software (virus and spyware)
-
 44:00
44:00
removing spyware and malware from a windows pc using spybot search and destroy
-
 40:12
40:12
linux access control examples (its335, l09, y15)
-
 1:12:24
1:12:24
introduction to it security (its335, l01, y15)
-
 1:01:16
1:01:16
mitm attack and digital certificates (its335, l20, y15)
-
 13:10
13:10
insecurity of http (its335, l19, y15)
-
 1:04:18
1:04:18
assumptions of encryption and authentication (its335, l04, y15)
-
 1:04:25
1:04:25
access control (its335, l08, y15)
-
 27:59
27:59
introduction to internet privacy options (its335, l23, y15)
-
 7:25
7:25
hcl investigates ransomware, agent tesla returns, javascript bank malware
-
 1:07:07
1:07:07
message authentication codes (css441, l16, y15)
-
 1:10:52
1:10:52
internet security (its335, l22, y15)
-
 1:14:25
1:14:25
ping flooding dos attacks (its335, l13, y15)