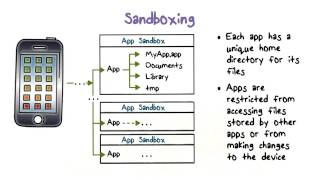
malware protection techniques: endpoint sandboxing
Published 11 years ago • 4.4K plays • Length 11:03Download video MP4
Download video MP3
Similar videos
-
 6:10
6:10
malware protection techniques: sandboxing and emulation
-
 13:37
13:37
malware protection techniques: network-based malware defense
-
 7:02
7:02
malware protection techniques (part 1): overview
-
 7:31
7:31
malware protection techniques: spectrum-based
-
 9:18
9:18
malware protection techniques - whitelisting
-
 6:55
6:55
how to protect yourself from mobile malware attacks
-
 5:43
5:43
how malware works? most common malware & how they work?
-
 2:14
2:14
how are more sophisticated ransomware attacks bypassing security defenses?
-
 8:39
8:39
malware protection techniques (part 4): behavioral-based
-
 8:30
8:30
malware protection techniques (part 3): heuristics
-
 2:20
2:20
sourcefire fireamp 5: advanced malware protection video 4 - outbreak control
-
 2:16
2:16
advanced malware protection: file trajectory
-
 2:34
2:34
sourcefire fireamp advanced malware protection demo video
-
 14:56
14:56
malware protection techniques (part 2): signatures
-
 1:30
1:30
sourcefire advanced malware protection: right in the middle of...
-
 2:19
2:19
advanced malware protection for firepower: overview
-
 1:27
1:27
sandboxing
-
 3:16
3:16
advanced malware protection: indications of compromise
-
 1:53
1:53
sourcefire advanced malware protection: enough of that
-
 2:08
2:08
what is cisco's advanced malware protection?