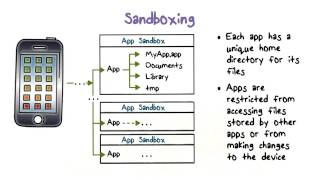
malware protection techniques: sandboxing and emulation
Published 11 years ago • 6.2K plays • Length 6:10Download video MP4
Download video MP3
Similar videos
-
 11:03
11:03
malware protection techniques: endpoint sandboxing
-
 13:37
13:37
malware protection techniques: network-based malware defense
-
 7:02
7:02
malware protection techniques (part 1): overview
-
 7:31
7:31
malware protection techniques: spectrum-based
-
 9:18
9:18
malware protection techniques - whitelisting
-
 10:30
10:30
what is malware? the most common types, how they work, & how to easily avoid them all
-
 10:08
10:08
what is malware and types of malware | introduction to malware | cyber security training|simplilearn
-
 5:41
5:41
the internet is a dangerous place - how malware attacks work
-
 8:39
8:39
malware protection techniques (part 4): behavioral-based
-
 8:30
8:30
malware protection techniques (part 3): heuristics
-
 14:56
14:56
malware protection techniques (part 2): signatures
-
 1:27
1:27
sandboxing
-
 18:17
18:17
how to setup a sandbox environment for malware analysis
-
 8:03
8:03
how anti-malware vendors work (part 2): sample collection
-
 10:56
10:56
what is sandboxing and why do you need it?
-
 21:10
21:10
detection of advanced attacks with a cpu level sandbox technology
-
 43:48
43:48
slime: automated anti-sandboxing disarmament system
-
 7:11
7:11
day-233: how can you detect sandbox-evading malware?
-
 29:18
29:18
defeating sandbox evasion: how to increase successful emulation rate in your virtualized environment
-
 1:58
1:58
sandboxing, what's that?
-
 24:56
24:56
a network sandbox for ics malware