malware protection techniques (part 2): signatures
Published 12 years ago • 7.3K plays • Length 14:56Download video MP4
Download video MP3
Similar videos
-
 8:30
8:30
malware protection techniques (part 3): heuristics
-
 7:02
7:02
malware protection techniques (part 1): overview
-
 8:39
8:39
malware protection techniques (part 4): behavioral-based
-
 9:18
9:18
malware protection techniques - whitelisting
-
 7:31
7:31
malware protection techniques: spectrum-based
-
 13:37
13:37
malware protection techniques: network-based malware defense
-
 6:10
6:10
malware protection techniques: sandboxing and emulation
-
 1:30
1:30
sourcefire advanced malware protection: right in the middle of...
-
 2:36
2:36
how to run antivirus scan on samsung galaxy s23's
-
 7:21
7:21
what is anti malware protection - microsoft defender for office 365 | anti malware engine
-
 37:37
37:37
aws re:inforce 2024 - fully managed malware and antivirus protection for amazon s3 (tdr204-new)
-
 8:03
8:03
how anti-malware vendors work (part 2): sample collection
-
 8:58
8:58
the evolution of anti-malware protection
-
 2:20
2:20
sourcefire fireamp 5: advanced malware protection video 4 - outbreak control
-
 6:00
6:00
rootkits (part 7): signature-based defense
-
 13:36
13:36
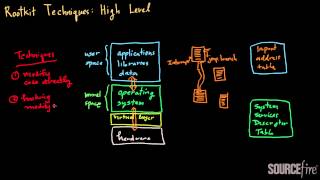
rootkits (part 2): high-level techniques
-
 7:24
7:24
history of computer viruses (part 2)
-
 10:31
10:31
evolution of computer viruses (part 2)
-
 5:07
5:07
ransomware defense series part two: the protect phase
-
 0:58
0:58
protect your business success, assets, and revenue with cyber security
-
 0:41
0:41
vipersoftx infostealer uses sophisticated techniques to avoid detection