usenix security '19 - understanding and securing device vulnerabilities through
Published 4 years ago • 409 plays • Length 19:12Download video MP4
Download video MP3
Similar videos
-
 21:31
21:31
usenix security '19 - discovering and understanding the security hazards in the
-
 12:07
12:07
usenix security '20 - understanding security mistakes developers make: qualitative analysis...
-
 20:43
20:43
usenix security '19 - understanding and improving security and privacy in multi-user
-
 17:50
17:50
usenix security '19 - looking from the mirror: evaluating iot device security through
-
 10:39
10:39
security testing with snyk.io || scan security issues directly from code
-
 2:16
2:16
what is a vulnerability?
-
 11:48
11:48
usenix security '23 - xnids: explaining deep learning-based network intrusion detection systems...
-
 1:42:14
1:42:14
usenix security '19 - security educational panel
-
 12:51
12:51
usenix security '22 - how long do vulnerabilities live in the code? a large-scale empirical...
-
 11:44
11:44
usenix security '22 - fugio: automatic exploit generation for php object injection vulnerabilities
-
 19:40
19:40
usenix security '19 - the knob is broken: exploiting low entropy in the encryption key
-
 10:45
10:45
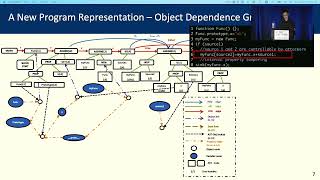
usenix security '22 - mining node.js vulnerabilities via object dependence graph and query
-
 49:18
49:18
usenix security '19 - evaluating mobile messengers for implementation vulnerabilities
-
 12:13
12:13
usenix security '21 - exposing new vulnerabilities of error handling mechanism in can
-
 20:01
20:01
usenix security '19 - leaky images: targeted privacy attacks in the web
-
 17:51
17:51
usenix security '19 - pac it up: towards pointer integrity using arm pointer authentication
-
 54:55
54:55
usenix security '19 - lessons learned about building secure software: it's about the developers!
-
 18:44
18:44
usenix security '19 - terminal brain damage: exposing the graceless degradation in deep
-
 23:23
23:23
usenix security '19 - wireless attacks on aircraft instrument landing systems
-
 18:34
18:34
usenix security '19 - birthday, name and bifacial-security: understanding passwords